Adding Governance to Your CI/CD Pipeline Without Slowing It Down
Governance does not have to be a bottleneck. Run it in parallel with your tests, generate evidence asynchronously, and gate deployment without adding latency.
Your CI pipeline has a governance-shaped hole in it. Code goes in, tests run, artifacts deploy. At no point does anyone verify that the change was risk-classified, reviewed against your security policies, or sealed into an evidence trail. Your pipeline proves the code works. It proves nothing about whether the code should have shipped.
Every engineering manager I pitch this to says the same thing: “We cannot add another step. Our pipeline is already 12 minutes.” They are right that latency kills adoption. They are wrong that governance is “another step.” That framing — governance as a sequential gate you bolt onto the end — is exactly why most teams either skip it or resent it.
Governance runs in parallel. Same trigger, same PR event, zero additional seconds on your critical path. When done right, it finishes before your integration tests do.
The Sequential Fallacy
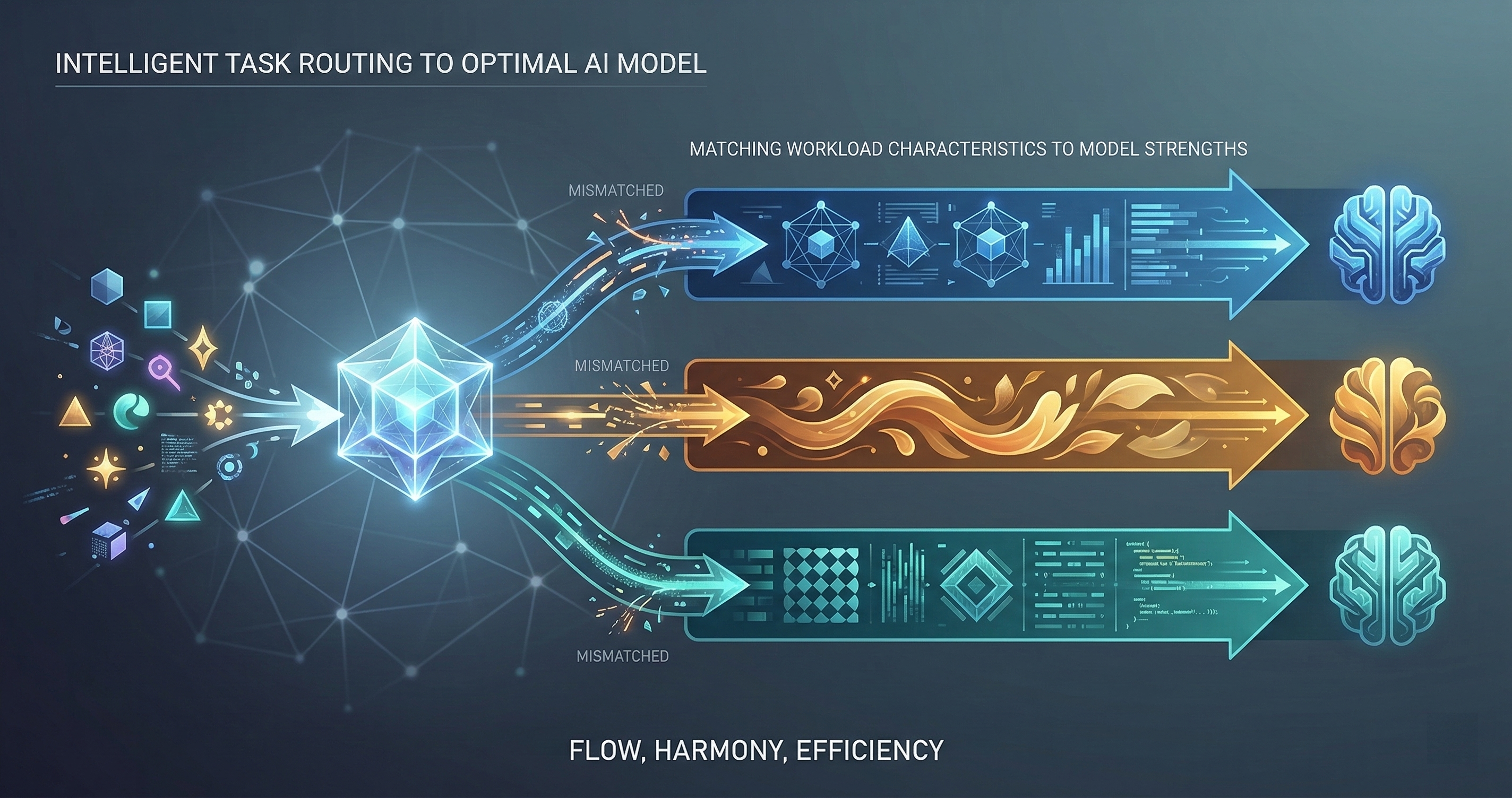
Most people picture CI/CD as a conveyor belt. Code goes in one end, steps execute one after another, and a deployable artifact comes out the other end. Lint, then unit tests, then integration tests, then security scan, then deploy. Each step waits for the previous one.
When you say “add governance,” they hear “add another step to the conveyor belt.” That mental model is wrong.
Modern CI systems — GitHub Actions, GitLab CI, Jenkins Pipeline — all support parallel job execution. Your unit tests do not wait for your linter. Your security scan does not wait for your integration tests. Governance should not wait for any of them.
GuardSpine’s GitHub Action runs as a parallel job from the moment a PR opens. While your test suite is running, GuardSpine is triaging the diff, assigning a risk tier, routing to AI reviewers, and generating an evidence bundle. By the time your tests finish, governance is already done.
The Architecture: Fan-Out, Gate-In
Here is the pattern:
jobs:
tests:
runs-on: ubuntu-latest
steps:
- run: npm test
governance:
runs-on: ubuntu-latest
steps:
- uses: DNYoussef/codeguard-action@v1
with:
risk_threshold: L2
deploy:
needs: [tests, governance]
runs-on: ubuntu-latest
steps:
- run: ./deploy.sh
Three jobs. tests and governance start simultaneously. deploy waits for both. The total pipeline time is max(tests, governance), not tests + governance.
In practice, GuardSpine finishes in 30-90 seconds for most PRs. Your test suite probably takes longer. Governance adds exactly zero seconds to your pipeline duration.
The deployment gate is the critical piece. Both jobs must pass before code ships. But they run at the same time. This is the difference between governance as a bottleneck and governance as a safety net.
Async Evidence Generation
Evidence bundles are the most expensive part of governance — they involve multiple AI model calls, hash chain computation, and cryptographic signing. But you do not need the evidence bundle before the deployment decision.
The decision — approve, reject, or escalate — happens fast. The risk tier is computed from the diff size, files touched, and pattern matching. The AI review calls run in parallel across models. The verdict is available in seconds.
The evidence bundle is generated asynchronously after the verdict. It seals the diff, the reviews, the policy evaluations, and the rationale into a cryptographically signed package. This bundle is stored for audit purposes. It does not block deployment.
Think of it like a restaurant receipt. The meal is served. The receipt prints afterward. If the receipt printer is slow, you do not wait to eat.
Non-Blocking vs. Non-Enforcing
I want to be precise about terminology because it matters.
Non-blocking means governance does not add wall-clock time to your pipeline. The governance job runs in parallel with everything else.
Non-enforcing means governance results are advisory only. A failure does not prevent deployment.
These are different things. GuardSpine is non-blocking but enforcing by default. It runs fast enough that it finishes before your tests, and it gates deployment if the risk threshold is exceeded.
You can configure it as non-enforcing for gradual rollout. Run it for two weeks in advisory mode, review the results, tune the policies, then flip the switch. This is how most teams adopt it. Nobody trusts a new gate on day one. Earn trust first, then enforce.
GitLab CI Configuration
GitLab uses stages, but stages can contain parallel jobs:
stages:
- validate
- deploy
test:
stage: validate
script: npm test
governance:
stage: validate
image: ghcr.io/dnyoussef/codeguard-action:latest
script: codeguard review --risk-threshold L2
deploy:
stage: deploy
script: ./deploy.sh
only:
- main
Both test and governance run in the validate stage simultaneously. The deploy stage waits for all validate jobs to pass.
Jenkins Pipeline
Jenkins Declarative Pipeline supports parallel stages natively:
pipeline {
stages {
stage('Validate') {
parallel {
stage('Tests') {
steps { sh 'npm test' }
}
stage('Governance') {
steps { sh 'codeguard review --risk-threshold L2' }
}
}
}
stage('Deploy') {
steps { sh './deploy.sh' }
}
}
}
Same pattern. Different syntax. The principle is identical: fan out for validation, gate in for deployment.
What About Monorepos?
Monorepos amplify the benefit. In a monorepo, a single PR might touch files across five services. Without governance, a senior engineer has to mentally model the blast radius across all five. With GuardSpine, each affected service gets its own risk assessment, and the overall PR risk is the maximum of the individual service risks.
GuardSpine’s monorepo support uses path-based policy routing. Changes to services/auth/ apply the security-critical policy. Changes to services/docs/ apply the low-risk policy. Changes that span both get the higher risk tier. The configuration lives in a single .guardspine.yml at the repo root.
This is where governance actually speeds up the review process. Instead of a senior engineer spending 45 minutes understanding a cross-service PR, they read the governance summary: “Auth service changes flagged L3, docs changes flagged L0, overall L3, three AI reviewers approved with comments on the auth token rotation logic.” Five seconds to triage what used to take an hour.
Measuring the Impact
After you add governance, track three numbers:
-
Pipeline duration delta. Measure your P50 and P95 pipeline times before and after. If governance is truly parallel, the delta should be near zero.
-
Deployment gate rate. What percentage of PRs are blocked by governance? If it is above 10%, your policies are too strict. If it is below 1%, your policies are too loose. The sweet spot is 3-7%.
-
Mean time to evidence. How long after a deployment can you produce a complete evidence bundle for audit? With async generation, this should be under 5 minutes.
These numbers tell you whether governance is a net positive or a drag. If your pipeline got slower, you configured it wrong. If your gate rate is zero, you are not governing anything. If evidence takes hours, your async pipeline is broken.
Start Today
Install the CodeGuard GitHub Action in advisory mode. Run it for two weeks. Review the results. Tune the risk thresholds. Then enforce.
Your pipeline will not get slower. Your audit trail will get dramatically better. And the next time compliance asks “how do you review AI-generated code,” you will have an answer with cryptographic proof.
Book a walkthrough if you want help configuring governance for your specific CI/CD setup.