n8n Workflow Integration: GuardSpine as Workflow Nodes
You already automate deployments and tests. Why aren't you automating governance? Eleven n8n nodes turn every workflow into a governed pipeline.
You already automate deployments. You already automate tests. Why aren’t you automating governance?
Every DevOps team I talk to has the same setup. Code gets pushed, CI runs, tests execute, containers build, deployment happens. Automated from commit to production. Then someone asks “who approved this change?” and the answer is a Slack thread from three weeks ago.
Eleven n8n nodes turn every workflow into a governed pipeline.
Governance Is the Gap in Your Automation
You automated builds because manual builds were slow and error-prone. You automated tests because manual testing missed regressions. You automated deployment because manual deploys caused outages.
Governance is still manual. Someone reviews a PR. Someone clicks approve. Someone writes a Jira comment. The evidence that this review happened lives in five different systems, none of which talk to each other, and none of which produce a tamper-evident audit trail.
n8n already connects your systems. GuardSpine nodes add governance to those connections. Instead of building governance as a separate process that runs alongside your automation, you embed it directly into the automation.
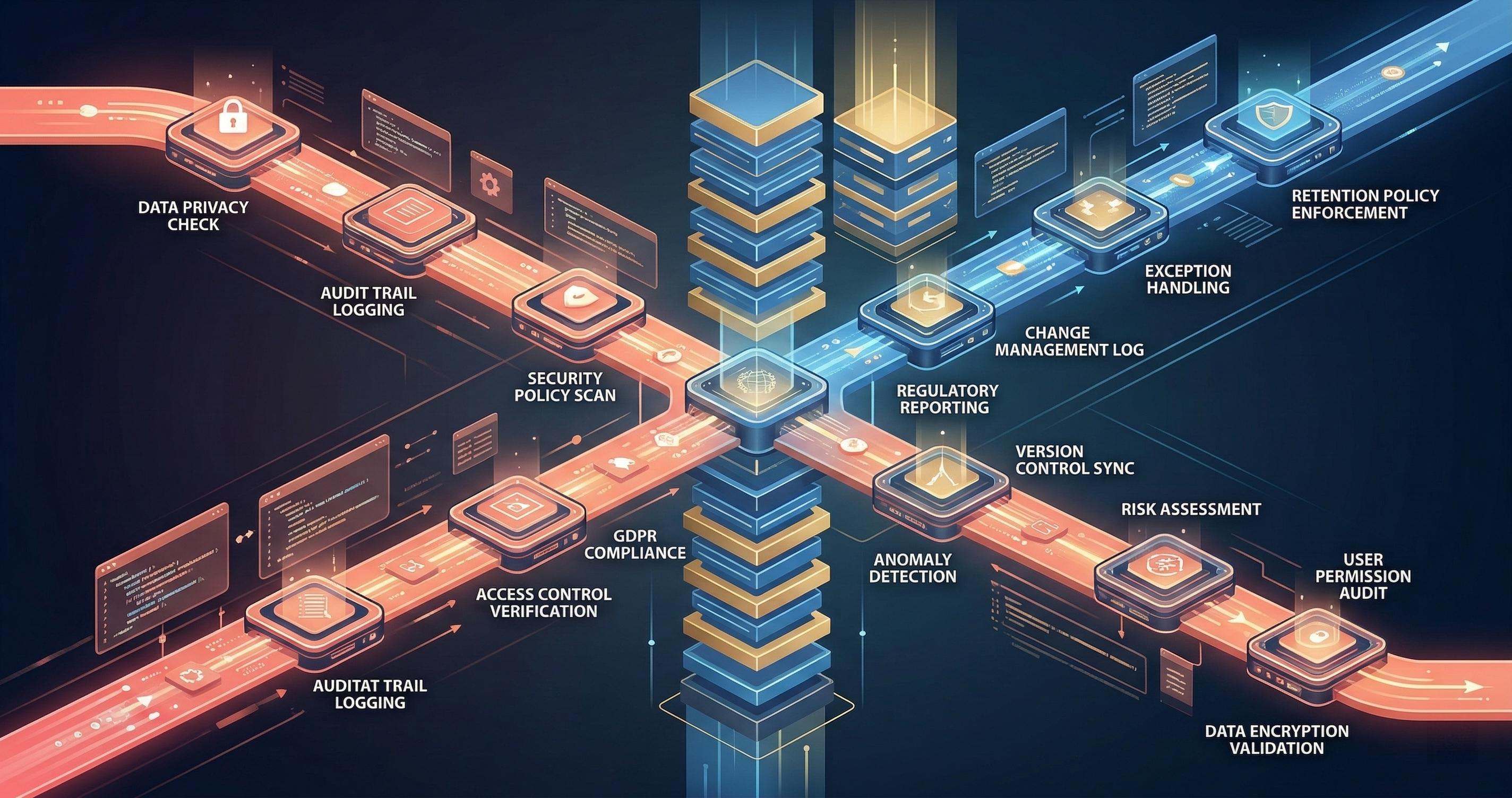
The Eleven Nodes
Each node handles one governance function. You compose them like any other n8n workflow.
CodeGuard
The core review node. Takes a diff (from GitHub, GitLab, Bitbucket, or raw text) and runs it through risk tier classification and AI review. Outputs a structured review result with findings, risk tier, and evidence.
Configuration: model selection, risk tier thresholds, rubric pack (HIPAA, SOC2, PCI-DSS, or custom). The node handles the diff parsing, model routing, and evidence formatting. You configure it once.
PDFGuard
Document governance. Takes a PDF and its previous version, diffs the content, and reviews changes. Tracks what changed between document versions — added paragraphs, removed sections, modified figures.
Use case: regulated document management. A clinical trial protocol changes. A compliance policy updates. A financial report revises a figure. PDFGuard captures exactly what changed and why.
SheetGuard
Spreadsheet governance. Takes a spreadsheet (XLSX, CSV) and diffs it cell by cell against the previous version. Identifies formula changes, value modifications, structural changes (added/removed rows and columns).
Use case: financial model review. A quarterly forecast changes three assumptions. SheetGuard flags which cells changed, what the old values were, and whether the formulas downstream still make sense.
ImageGuard
Visual asset governance. Compares images using perceptual hashing and pixel-level diffing. Detects modifications to screenshots, diagrams, marketing materials, and UI mockups.
Use case: brand compliance. A marketing team updates a product screenshot. ImageGuard verifies the changes align with brand guidelines and produces evidence of what was modified.
GuardGate
Decision routing based on risk tier. Takes a GuardSpine review result and routes the workflow based on the risk level. L0-L1 goes left (auto-approve). L2 goes middle (notify). L3-L4 goes right (block and escalate).
This is the branching node. It replaces the manual decision of “does this need a human?” with a policy-driven gate.
EvidenceSeal
Takes all the evidence from upstream nodes and seals it into a tamper-evident bundle. Computes the hash chain, adds timestamps, includes the review results and the original artifact.
The sealed bundle is the audit artifact. Export it as JSON, SARIF, or ZIP. Store it in your artifact repository, S3 bucket, or compliance system.
CouncilVote
Multi-model consensus node. Sends a review task to multiple AI models and aggregates their votes. Configurable consensus type: UNANIMOUS, SUPERMAJORITY, MAJORITY, PLURALITY.
Use this when a single model’s opinion isn’t enough. Three models review the same change. The council votes. Disagreements get flagged. Consensus gets recorded.
ApprovalWait
Human-in-the-loop pause. The workflow stops and waits for a human to approve or reject. Sends a notification (Slack, email, Teams) with the review context. Resumes when the human responds.
Use this for L3-L4 changes where automated review isn’t sufficient. The AI council flagged a concern. A senior engineer reviews the concern and decides. The decision is recorded in the evidence bundle.
BeadsCreate
Creates a project management bead (work unit) from workflow data. Links the governance evidence to project tracking. Every governed change gets a bead that tracks its lifecycle.
BeadsUpdate
Updates an existing bead with new status, evidence, or metadata. As a change moves through review, approval, and deployment, the bead accumulates the full history.
GuardSpineCompress
Compression node for large evidence bundles. When a workflow generates substantial evidence (multiple reviews, large diffs, image comparisons), this node compresses the bundle for efficient storage without losing verifiability.
The Standard Pattern
Most teams start with the same workflow pattern and customize from there.
PR Opened
-> CodeGuard (review the diff)
-> GuardGate (route by risk tier)
-> L0-L1: EvidenceSeal -> Auto-merge
-> L2: CouncilVote -> EvidenceSeal -> Notify reviewer
-> L3-L4: CouncilVote -> ApprovalWait -> EvidenceSeal -> Block until approved
This pattern handles 90% of cases. Low-risk changes flow through automatically with evidence. Medium-risk changes get multi-model review and human notification. High-risk changes require both AI consensus and human approval before proceeding.
The key insight: every path produces an evidence bundle. The auto-approved L0 change and the heavily-reviewed L4 change both generate tamper-evident audit artifacts. The level of scrutiny differs. The evidence trail doesn’t.
Advanced Patterns
Multi-Artifact Governance
A release isn’t just code. It includes documentation, configuration, database migrations, and sometimes regulatory filings. One workflow governs all of them:
Release Trigger
-> [parallel]
-> CodeGuard (code changes)
-> PDFGuard (documentation changes)
-> SheetGuard (config spreadsheet changes)
-> GuardGate (highest risk tier from any guard)
-> CouncilVote (if L2+)
-> EvidenceSeal (combined bundle)
-> BeadsCreate (release bead)
The GuardGate takes the highest risk tier from any of the parallel guards. If the code is L1 but the config spreadsheet change is L3, the whole release gets L3 treatment. The weakest link determines the scrutiny level.
Nomotic Interrupt Handling
Nomotic mode adds governance semantics to workflows. A nomotic interrupt fires when a governance boundary is violated — an unauthorized user attempts an L4 change, a review timeout expires, or a quorum isn’t met.
The interrupt node catches these events and routes them to the appropriate handler. Instead of the workflow failing silently, it escalates visibly.
Any Guard Node
-> on_nomotic_interrupt
-> Log violation
-> Notify governance team
-> Block workflow
-> BeadsUpdate (record violation)
Scheduled Governance Audits
Not all governance is triggered by changes. Some is periodic. A weekly workflow scans all repositories for ungoverned changes — commits that bypassed the PR process, direct pushes to main, force merges without review.
Weekly Schedule
-> Scan repos for ungoverned commits
-> CodeGuard (retroactive review)
-> EvidenceSeal (flag as retroactive)
-> Notify compliance team
Retroactive evidence isn’t as strong as real-time evidence. But it’s better than no evidence. And it identifies process gaps — if the same developer keeps bypassing the PR process, that’s a conversation to have.
Why n8n and Not Custom Code
You could build all of this with scripts. I know because I did, before building the n8n nodes. The scripts worked. They were also unmaintainable.
n8n gives you three things that custom scripts don’t:
Visual workflow design. A compliance officer can look at the n8n workflow and understand the governance process. They can’t read a Python script. The visual representation IS the documentation.
Connector library. n8n has 400+ integrations. Your governance workflow can trigger Slack notifications, create Jira tickets, update Confluence pages, send emails, call webhooks, and store artifacts in S3 — all without writing connector code.
Error handling. n8n handles retries, timeouts, error branches, and dead letter queues. When Ollama times out or a model returns garbage, the workflow catches it and routes to a fallback. Building this in scripts means building your own retry logic, timeout handling, and error routing.
The governance nodes focus on governance. n8n handles everything else.
Getting Started
Install the GuardSpine n8n node package. Configure your model providers (Ollama for local, or cloud APIs if allowed). Build the standard pattern workflow. Run it against a test repository.
The first workflow takes 30 minutes to build. The evidence bundles start generating on the first PR. Your next audit has real evidence instead of reconstructed memories.
Governance that runs at the speed of your automation. Not alongside it. Inside it.
Want to see the n8n nodes in action against your existing workflows? Book a call and bring your current CI/CD setup. I’ll show you where governance nodes fit.