Scaling Governance: From One Repo to a Thousand
What changes when you go from governing one repository to governing an entire organization. Centralized policy, per-team overrides, and role-based escalation.
You governed one repo. Your VP saw the evidence bundles and said, “Roll this out to every repo in the org.” Six weeks later, your payment service has different review rules than your auth service, nobody can explain why, and three teams have silently disabled the governance checks because they were “slowing down deploys.”
Congratulations. You just learned that scaling governance is not a technical problem. It is an organizational failure mode. And most teams discover this the expensive way — during an audit, when someone asks why repo 37 out of 200 has no evidence bundles for the last quarter.
I have watched this pattern repeat enough times to know the fix. It is not “try harder with config files.”
The First Repo Is Free
When a team installs GuardSpine on their first repository, everything is simple. One .guardspine.yml file. One set of policies. One risk threshold. The team owns the config, understands the output, and iterates fast. Time to value: about fifteen minutes.
Then their VP of Engineering sees the evidence bundles and says, “I want this on every repo in the org.” That is when the real work starts. With the EU AI Act enforcement hitting August 2, 2026, that conversation is happening sooner than most teams expected. The orgs that already have governance at scale will answer the compliance question in minutes. The rest will answer it in months.
The naive approach is to copy the config file to every repository. This breaks within a week. Team A needs stricter rules for their payment service. Team B wants to exclude their documentation repo. Team C has a custom model they want in the review council. Meanwhile, the security team wants a baseline that nobody can override.
Copy-paste governance does not scale. Inheritance does.
Centralized Policy Management
GuardSpine uses a policy hierarchy with three levels:
Organization policy lives in a dedicated policy repository. It defines the baseline that every repository in the org must meet. Minimum risk tier for deployment gates. Required reviewers for L3+ changes. Mandatory evidence bundle fields. This is the security team’s territory.
Team policy extends the org policy with team-specific rules. The payments team raises their default risk threshold. The internal tools team lowers theirs. Team policies can tighten org policy but cannot weaken it. A team cannot disable a gate that the org policy requires.
Repository policy is the local .guardspine.yml. It handles path-based routing, custom model selection, and repository-specific exclusions. Like team policy, it can tighten but not weaken.
The enforcement rule is simple: the effective policy for any PR is the union of all three levels, with conflicts resolved by taking the stricter option. If the org says L2 minimum and the team says L3 minimum, the effective threshold is L3. If the repo says L1 minimum, the org’s L2 overrides it.
This hierarchy means the security team sets the floor, teams adjust for their risk profile, and individual repos handle their quirks. Nobody copies config files. Nobody drifts.
Per-Team Overrides Without Chaos
The fear with overrides is that they become escape hatches. Every team requests an exception, and within six months the “centralized” policy is Swiss cheese.
GuardSpine handles this with typed overrides. A team override is not a freeform YAML blob. It is a structured object with a specific set of fields that can be modified:
team_overrides:
risk_threshold: L3 # Can raise, not lower
review_models: ["claude-sonnet-4", "gpt-4o"] # Can add, not remove org-required models
excluded_paths:
- "*.md" # Can exclude low-risk paths
- "test/**" # But not paths the org policy marks as critical
The schema enforces what can change and what cannot. The org policy can mark specific fields as locked, meaning no team or repo can override them. Authentication logic always gets L4 review. PII-handling code always includes the privacy model in the council. These are non-negotiable.
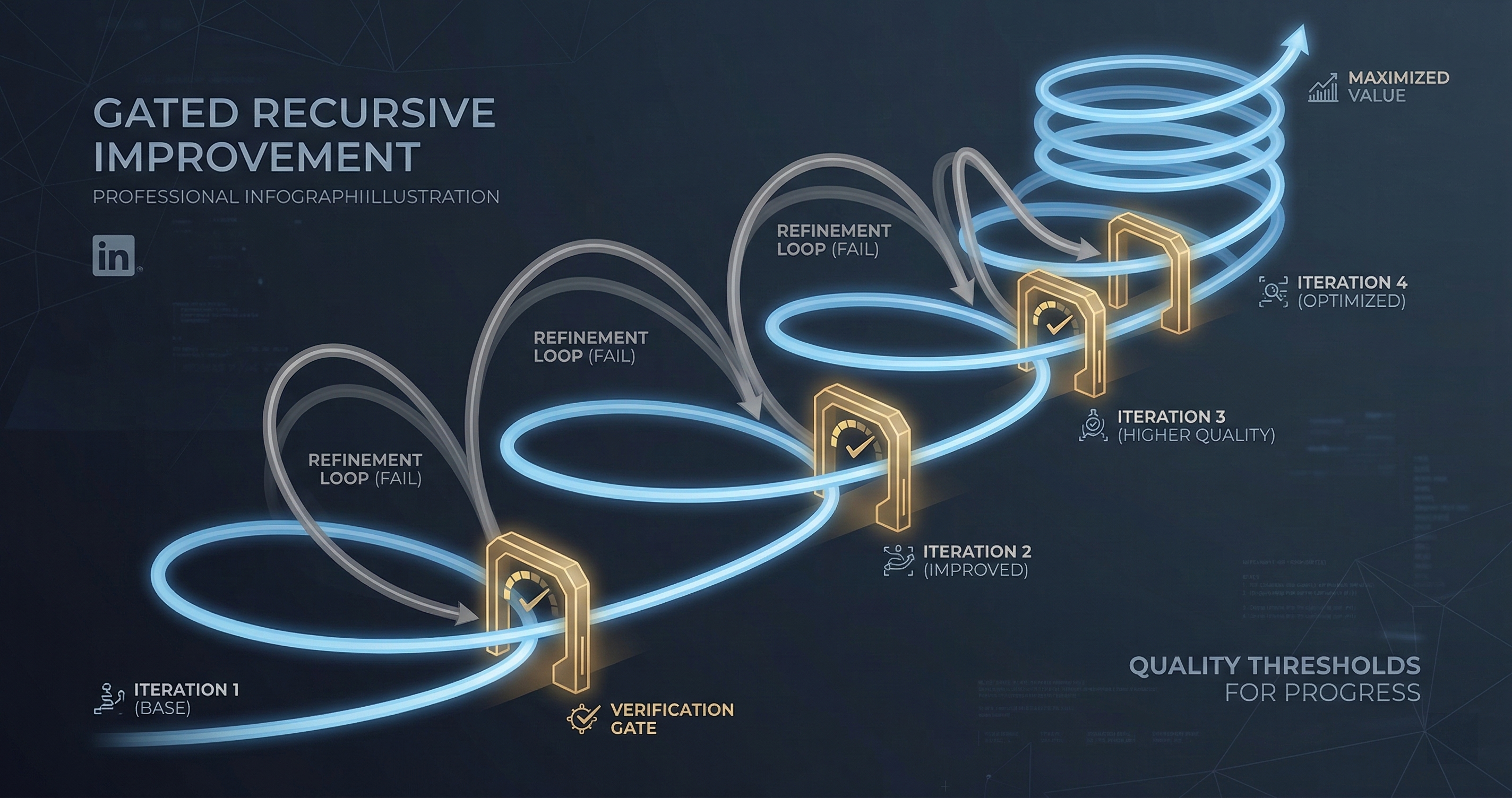
When a team submits an override request, it goes through the same governance process. The override itself is a diff. It gets reviewed, risk-tiered, and sealed into an evidence bundle. Governance governing governance. That is not recursion for fun — it is the only way to maintain auditability at scale.
Role-Based Escalation
At scale, not every governance decision should reach the same person. L0 changes to documentation should auto-approve. L4 changes to authentication logic should escalate to the security lead. L2 changes to a junior developer’s first PR should escalate to their team lead.
GuardSpine’s escalation model uses three dimensions:
Risk tier determines the base escalation level. L0-L1 auto-resolve. L2 requires one human reviewer. L3 requires a senior reviewer. L4 requires a security team sign-off.
Author context modifies the escalation. New contributors get one tier higher for their first ten PRs. Contributors with a history of governance violations get one tier higher until they clear the threshold.
Change context further modifies. Changes touching files that have had security incidents in the last 90 days get one tier higher. Changes that span multiple services get one tier higher. These stack, but cap at L4.
The result is a system where most PRs resolve automatically, some require a quick human glance, and a small number get serious review. In our early enterprise deployments, the breakdown is roughly 60% auto-resolve, 30% single reviewer, 8% senior reviewer, 2% security escalation. Those numbers are sustainable. Every PR requiring senior review is not.
The Dashboard Problem
Once you govern a thousand repos, you need to see what is happening. Individual PR comments are not enough. You need aggregate visibility.
GuardSpine’s org dashboard answers five questions:
-
Coverage: What percentage of repos have governance enabled? What percentage of PRs go through governance? Gaps are risks.
-
Risk distribution: How many L0, L1, L2, L3, L4 changes this week? A sudden spike in L3+ changes means something changed in the codebase or the team.
-
Review velocity: How long between PR open and governance verdict? If this is growing, you are falling behind.
-
Override frequency: How many team or repo overrides were requested this month? Rising override requests mean your base policy is too strict or too generic.
-
Evidence completeness: What percentage of bundles have all required fields? Incomplete bundles are compliance debt.
These metrics are not decorative. They are operational. The security team reviews them weekly. The engineering leadership reviews them monthly. They tell you whether governance is working or whether it is theater.
What Does Not Change
At a thousand repos, the fundamental architecture is the same as at one repo. Every PR gets a diff. Every diff gets risk-tiered. Every risk tier triggers appropriate review. Every review generates evidence. Every evidence bundle is cryptographically sealed.
The policy hierarchy adds organizational structure. The escalation model adds human judgment where it matters. The dashboard adds visibility. But the core loop — diff, tier, review, seal — is identical whether you govern one repository or ten thousand.
That is by design. Systems that require architectural changes at each order of magnitude are systems that break at each order of magnitude. The review loop scales horizontally. Add more repos, run more parallel jobs. The policy repo is read once per pipeline run. The evidence bundles are independent — no cross-repo coordination required.
Getting There
If you are governing one repo today and want to govern a hundred, here is the path:
- Create a policy repository. Move your current
.guardspine.ymlinto it as the org baseline. - Install the GuardSpine GitHub App (not the Action) at the org level. The App applies governance to every new repo automatically.
- Have each team submit their override requests as PRs to the policy repo. Review them.
- Deploy the dashboard. Set up weekly review with the security team.
- Monitor override frequency and evidence completeness for the first month. Adjust the base policy until override requests stabilize.
The whole migration takes about two weeks for a 100-repo org. Most of that time is policy tuning, not technical setup.
Book a call if you want to walk through the migration plan for your organization.