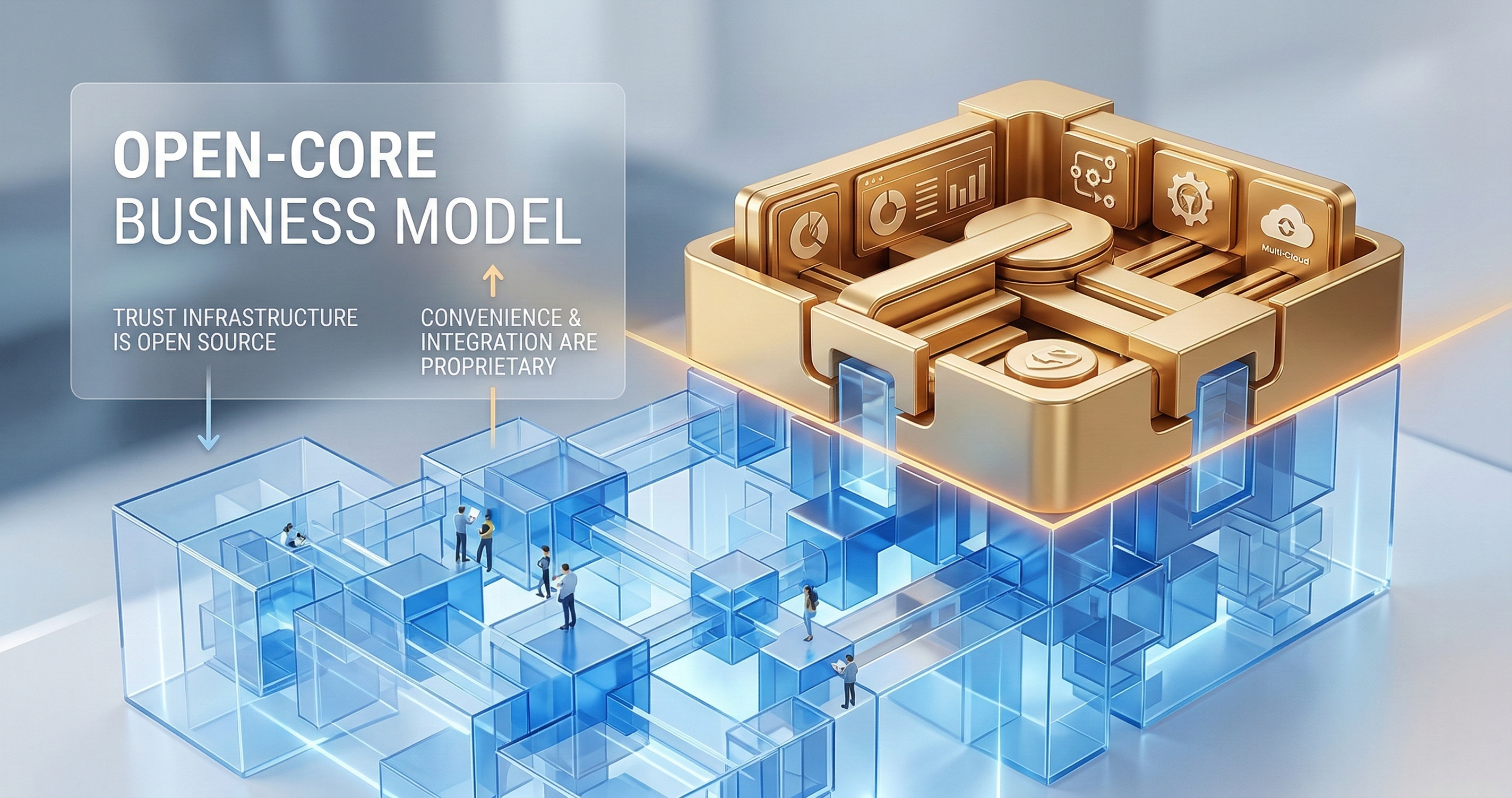
Trust Open, Convenience Private: The GuardSpine Business Model
The trust layer is Apache 2.0. Forever. The convenience layer is how we make money. Here's exactly where the line is, and why we drew it there.
The trust layer is Apache 2.0. Forever. The convenience layer is how we make money. Here’s exactly where the line is, and why we drew it there.
Open-core is a business model with a reputation problem. Too many companies use “open source” as a marketing label while keeping the important parts proprietary. The community builds on the open foundation, then discovers that the thing they actually need is behind a paywall. Trust erodes. Contributions dry up. The open source becomes a demo version.
We drew the line differently. The line isn’t between “free” and “paid.” It’s between “trust” and “convenience.”
Why the Line Matters
In governance, trust is the product. If your auditor can’t verify your evidence independently, the evidence is worthless. If your evidence format is proprietary, verification requires buying software. If verification requires buying software, the vendor controls the trust chain.
That’s broken. Trust should be verifiable by anyone, using tools that anyone can access, without paying anyone for the privilege.
Our boundary rule: everything required to verify trust is open source. Everything that makes trust more convenient to manage is the paid product.
You can verify evidence for free, forever. You can manage evidence at scale for a price.
The Six Immutable Boundary Rules
These rules are immutable. Not “immutable until we raise our Series B.” Not “immutable unless a competitor forces our hand.” Immutable. Permanently.
Rule 1: The Evidence Bundle Spec Stays Open
The evidence bundle format — the JSON schema, the hash chain specification, the signature format — is Apache 2.0 licensed. Anyone can read it, implement it, generate evidence in this format, and verify evidence in this format.
Why: the evidence spec IS the trust layer. If the spec is proprietary, only our tools can verify evidence. That makes us a gatekeeper of trust. Trust that requires a gatekeeper isn’t trustworthy.
The spec being open means competitors can build tools that generate and verify the same evidence format. Good. That makes the evidence more valuable, not less. An evidence format that only one tool produces is a vendor lock-in format. An evidence format that many tools produce is a standard.
Rule 2: The Verification CLI Stays Open
guardspine-verify is a command-line tool that verifies evidence bundles offline. Download it. Run it against an evidence bundle. Get a verification result: valid or invalid, with details about what was verified.
Why: an auditor who needs to install our commercial product to verify evidence is an auditor who depends on us. That dependency undermines the independence of the audit. The verification CLI removes the dependency. The auditor verifies with open-source tooling. Our commercial product is irrelevant to the verification.
Rule 3: The Kernel Stays Open
The GuardSpine kernel — the core logic that classifies risk tiers, evaluates rubrics, generates evidence, and computes hash chains — is Apache 2.0 licensed. Available in TypeScript and Python. Anyone can embed it in their own tools.
Why: the kernel is the engine of trust. If the engine is proprietary, trust depends on our continued existence as a company. If we get acqui-hired, shut down, or pivot, the trust engine disappears. An open kernel means the trust engine survives regardless of what happens to us.
Rule 4: The Connector SDK Stays Open
The SDK for building connectors — integrations that pipe data into and out of GuardSpine — is open source. Want to build a connector for your internal tool? Use the SDK. Want to sell a connector? Go ahead.
Why: governance needs to integrate with everything. We can’t build connectors for every internal tool at every organization. The SDK lets organizations build their own. Restricting the SDK restricts governance adoption. We want the opposite.
Rule 5: No Telemetry in OSS
The open-source components contain zero telemetry. No phone-home. No usage tracking. No anonymous metrics. Nothing.
Why: governance tools that report back to a vendor are a liability, not an asset. Especially for organizations in regulated industries, defense, or finance. The open-source components run in your environment without any external communication.
If you use the commercial product, we track usage metrics for billing and product improvement. We tell you exactly what we track. You agree to it explicitly. But the OSS components are silent. Permanently.
Rule 6: No License Keys for Verification
Verifying evidence never requires a license key, a subscription, an account, or an API call to our servers. Download the CLI. Verify. Done.
Why: if verification requires a license key, we can revoke verification capability. That means we can selectively allow or deny trust verification. That’s too much power for any vendor to hold over a governance system.
What’s Private: The Convenience Layer
Everything above is about trust. Trust generation, trust verification, trust interoperability. All open.
The private layer is about convenience. Making governance easier to manage at scale. This is where the product is. This is where we make money.
Approval Inbox
A centralized UI where approvers see all pending reviews across all repositories, all artifact types, and all risk tiers. Filtered, prioritized, and actionable.
You can manage approvals without it — through GitHub PR comments, Slack notifications, email. The Approval Inbox makes it faster. It doesn’t make it possible.
Approver Routing
Automatic routing of reviews to the right approver based on risk tier, file path, team ownership, and availability. On-call rotation integration. Escalation chains.
You can route approvals manually. The routing engine removes the manual step.
Evidence Bundle Registry
A searchable, indexed store of all evidence bundles across your organization. Query by date range, risk tier, repository, reviewer, finding type. Aggregate statistics. Compliance reporting.
You can store evidence bundles in S3 and search them with grep. The registry makes it usable at scale.
Policy Management UI
A visual interface for creating and modifying governance policies. Risk tier definitions, rubric packs, authority boundaries, conditional rules. Preview changes before deploying them.
You can write policies in YAML. The UI makes policy management accessible to compliance officers who don’t write YAML.
Org Analytics
Dashboards showing governance metrics across your organization. Review volume, risk tier distribution, catch rates, approval times, evidence completeness. Trends over time. Team comparisons.
You can compute these metrics from the evidence bundles. The analytics dashboard computes them for you.
SSO/SCIM
Enterprise identity integration. Your existing identity provider (Okta, Azure AD, Google Workspace) manages who has access to what in GuardSpine. User provisioning and deprovisioning syncs automatically.
You can manage users manually. SSO/SCIM makes it automatic and auditable.
Managed Connectors
Pre-built, maintained connectors for common platforms: Jira, ServiceNow, Confluence, Slack, Teams, PagerDuty, Splunk, Datadog. We build them, test them, update them when APIs change.
You can build your own connectors with the open SDK. Managed connectors save you the maintenance burden.
Why This Model Works
The trust/convenience split aligns incentives correctly.
For individual developers: The GitHub Action is open source. Install it. Get governed PRs. Verify evidence. No cost. No account. No catch. If governance is good enough to use for free, more people adopt it. More adoption means more evidence in the standard format. More evidence means the standard gains traction.
For teams: The open-source tools handle governance. The commercial tools handle management. A team of five developers probably doesn’t need the Approval Inbox — they can manage reviews in GitHub. A team of fifty needs it because the volume exceeds what informal processes handle.
For enterprises: The open-source kernel means no vendor lock-in on the trust layer. If we raise prices, change strategy, or disappear, the trust layer keeps working. The commercial layer is convenience. Convenience is worth paying for. It’s not worth being locked into.
For competitors: Build on the spec. Build on the kernel. Generate evidence in the same format. Compete with us on the convenience layer. The trust layer isn’t competitive territory — it’s shared infrastructure. The more tools that generate GuardSpine-format evidence, the more valuable the evidence format becomes.
For auditors: Verify evidence with open-source tools. No vendor account required. No commercial relationship required. Independent verification using independent tools. That’s what “independent audit” actually means.
What We Won’t Do
We won’t move the line. We won’t make the evidence spec proprietary in v2. We won’t add “advanced verification” features that require the commercial product. We won’t add telemetry to the OSS components.
These aren’t just commitments. They’re encoded in the license. Apache 2.0 is irrevocable. Code released under Apache 2.0 stays under Apache 2.0 forever. Even if we relicense future versions (we won’t, but hypothetically), the released versions remain open.
We also won’t do the bait-and-switch that gives open-core a bad name. We won’t release features as open source to gain adoption, then move them behind the paywall once they’re established. If it’s open today, it’s open tomorrow.
The Business Math
“But how do you make money if the core is free?”
The same way Red Hat makes money with Linux. The same way Elastic makes money with Elasticsearch. The same way HashiCorp makes money with Terraform. The core is free. The management, convenience, and enterprise features are paid.
Our pricing tiers:
Free/OSS. The kernel, the CLI, the GitHub Action, the evidence spec, the connector SDK. Unlimited use. Unlimited users. Unlimited repositories.
Team. Approval Inbox, basic analytics, email support. For teams that need management but not enterprise features.
Organization. Everything in Team plus Approver Routing, Evidence Registry, Policy Management UI, SSO/SCIM, managed connectors, and dedicated support.
Breakeven math: 3 Organization customers or 14 Team customers covers our monthly burn. We’re not building a charity. We’re building a business where the business model doesn’t undermine the product’s purpose.
Governance that requires trusting a vendor isn’t governance. It’s delegation. Our business model ensures that trust is independent of our commercial relationship. Verify for free. Manage for a price. Trust nobody — verify everything.
Want to see how the open-core model maps to your organization’s governance requirements? Book a call and I’ll walk you through the trust/convenience split for your use case.